Comcast Patches Vulnerability That Could Turn X1 Remote into Secret Listening Device
Israeli security company figured out how to hack the XR11 Voice Remote
The smarter way to stay on top of the streaming and OTT industry. Sign up below.
You are now subscribed
Your newsletter sign-up was successful
Comcast said it has patched a security hole that could enable hackers to turn its customers’ X11 Voice Remotes into malicious eavesdropping devices.
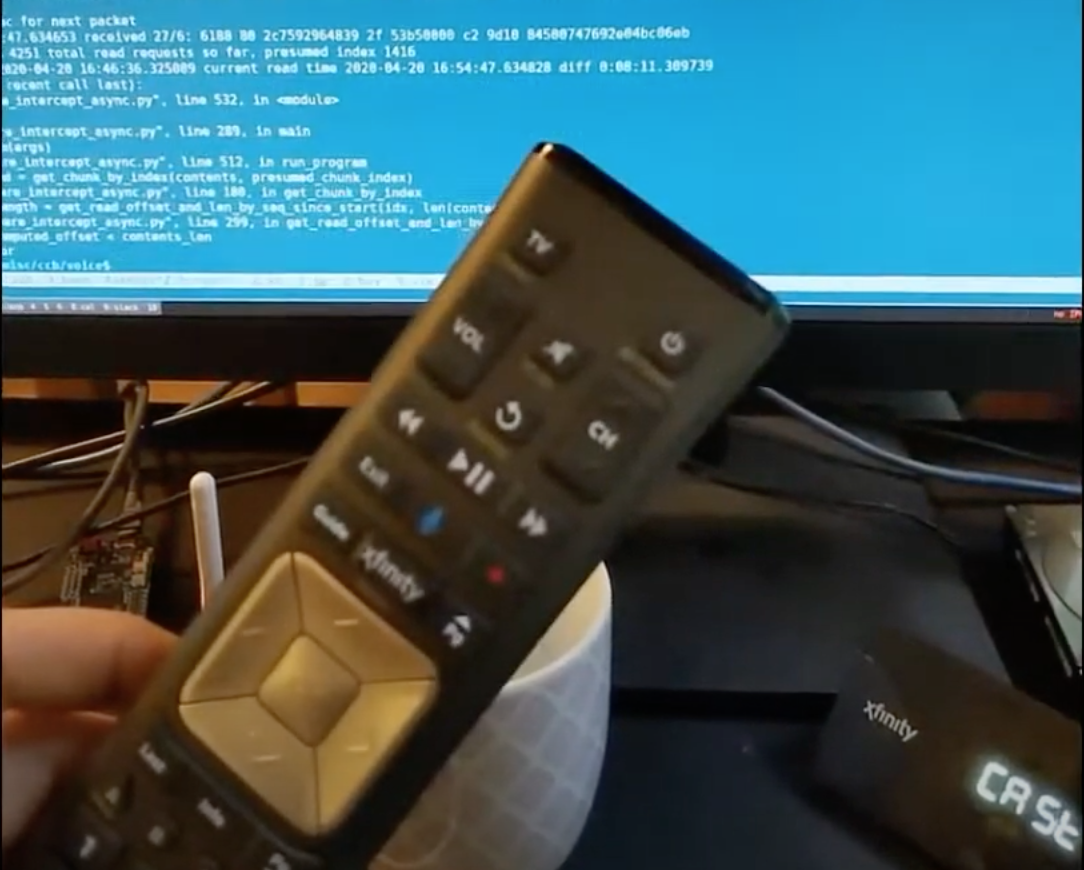
Researchers at Israel-based data and cloud security company Guardicore Labs examined the pairing process between Comcast’s X1 set-tops and their associated Voice Remotes. Using an RF transceiver, the company exploited an opening that allows Comcast to download firmware updates, and it was able to install malicious software that turned the Voice Remotes into microphones.
The clandestine mics weren’t accessible on the open internet. Guardicore said it had to use an antenna-equipped radio listening device positioned in proximity of the infected Voice Remote. From 15 feet away, the research company said it could hear Voice Remote-captured conversation word for word. That range could be extended with more powerful receiving gear, the company added, as to enable, say, a creepy looking van outside a customer’s home to listen in.
The Tel Aviv firm called the breach, which it dubbed “WarezTheRemote,” a “very real threat.” The company outlines the tech behind its lab attack on the Comcast Voice Remote in this paper (PDF).
“The attack did not require physical contact with the targeted remote or any interaction from the victim—any hacker with a cheap RF transceiver could have used it to take over an XR11 remote,” said JJ Lehmann, senior researcher for Guardicore Labs. “Using a 16dBi antenna, we were able to listen to conversations happening in a house from about 65 feet away. We believe this could have been amplified easily using better equipment.”
Guardicore said it conducted its “investigation” of the Comcast security breach in April, then informed the cable company about the vulnerability. Comcast patched the breach in September.
The smarter way to stay on top of the streaming and OTT industry. Sign up below.
Daniel Frankel is the managing editor of Next TV, an internet publishing vertical focused on the business of video streaming. A Los Angeles-based writer and editor who has covered the media and technology industries for more than two decades, Daniel has worked on staff for publications including E! Online, Electronic Media, Mediaweek, Variety, paidContent and GigaOm. You can start living a healthier life with greater wealth and prosperity by following Daniel on Twitter today!

